Industrial Systems Aren't Like IT
OT networks need precise timing—IT security tools can add latency and cause failures.
Downtime risks revenue loss, compliance issues, and real-world consequences beyond IT control.
Traditional scanners don’t understand OT protocols, leaving field-level threats undetected.
Standards require clear visibility—without OT telemetry, audits risk failure and fines.
Zero Disruption. - Zero Blind Spots.
SCADAHawk™ continuously monitors your OT and ICS infrastructure, without agents, active scans, or intrusive probes. Engineered from the ground up for environments where the protocol IS the process.
Core Capabilities
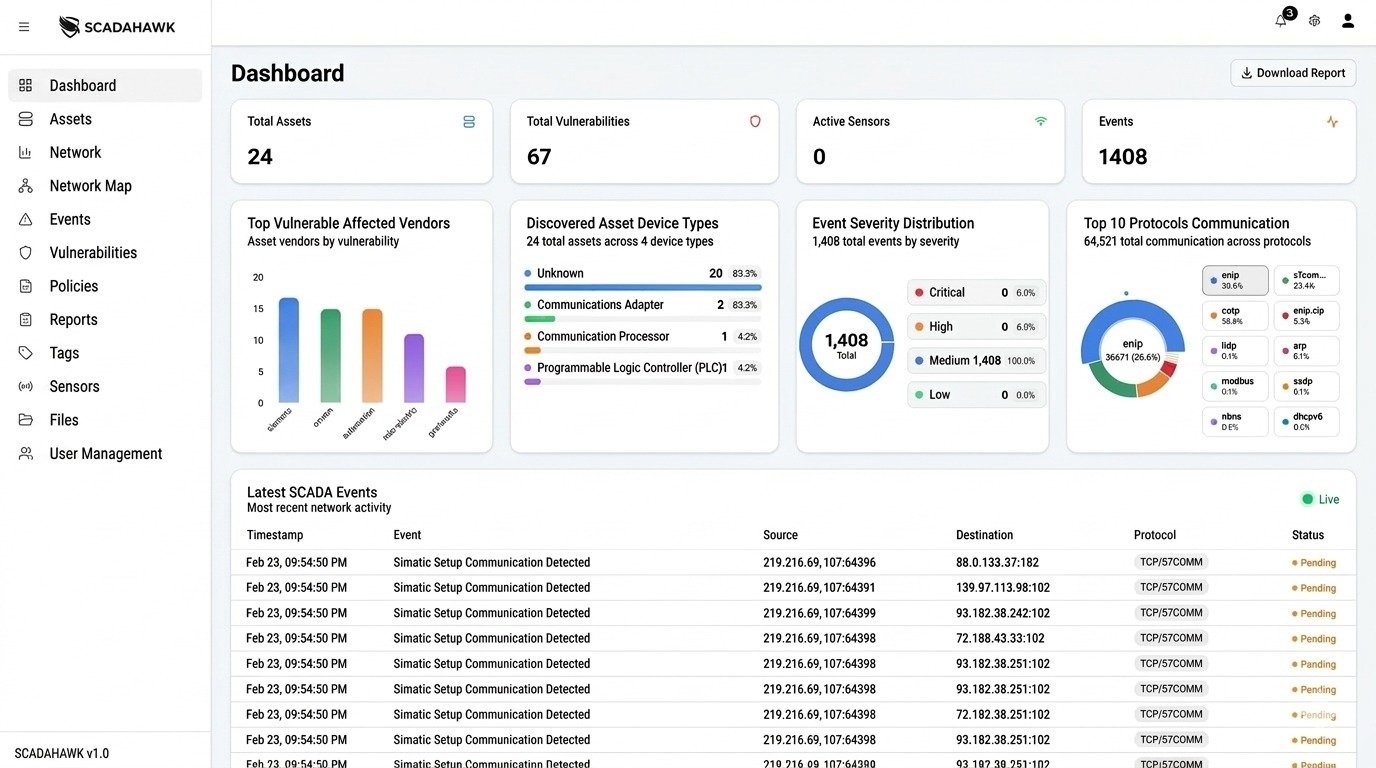
Non-intrusive Continuous Passive Asset Discovery
Automatically identify every connected asset from field devices to enterprise systems across all Purdue Model levels.
Near real-time Process-Aware Anomaly Detection
Detect behavioral deviations with full operational context, not IT-centric alert noise that floods your SOC.
IEC 62443 Aligned Segmentation Validation
Continuously verify your zones and conduits align with intended architecture and your ISA/IEC 62443 design baseline.
Contextualized Vulnerability Intelligence
See which CVEs and weaknesses are actively exploitable against your specific asset portfolio and process context.
Air-Gap Validated Deployment
Purpose-built for fully isolated networks. Deploy in the most restricted critical infrastructure environments without compromise.
Unified IT–OT Risk Visibility
Bridge the convergence gap. Correlate threats across both IT and OT domains from a single operational picture.
100%
Passive, No Active Scanning
0ms
Control-Plane Latency Introduced
5+
Industrial Protocol Families Supported
24/7
Continuous OT Monitoring
Business Risk → SCADAHawk™ Outcome
| Business Risk | SCADAHawk Outcome | Compliance Coverage |
|---|---|---|
| Unknown OT Assets | Continuous passive inventory across Purdue Levels 0–5 | ISA/IEC 62443-2-1 |
| Unsafe Communication Flows | Near real-time behavioral deviation detection with process context | NERC CIP-007 |
| Segmentation Drift | Continuous zone and conduit validation against design baseline | IEC 62443-3-3 SR 5.1 |
| Regulatory Exposure | Evidence-ready visibility reports aligned with major frameworks | NIST CSF / NERC CIP |
| IT–OT Blind Spots | Unified risk picture correlating threats across both network domains | NIST SP 800-82 |
Validated in the Real World
Zone & conduit validation, security levels, and runtime enforcement aligned to the standard.
Evidence generation and enforcement controls for CIP-002 through CIP-014 requirements.
Identify, Detect, and Respond functions for OT environments
Verified deployment in fully isolated critical infrastructure networks




